Turkish Travel Website Honeypot
Built a complete honeypot infrastructure disguised as a legitimate Turkish travel advice website. The system captures and logs attacker interactions while presenting a convincing front-end with real RSS-fed content, user registration flows, and an interactive comment system that serves as a trap for automated bots and manual attackers.
Tech Stack
The Problem
Organizations need to detect and study attack patterns on web applications, but setting up realistic honeypots requires significant effort to make them convincing enough to attract real threat actors.
Approach
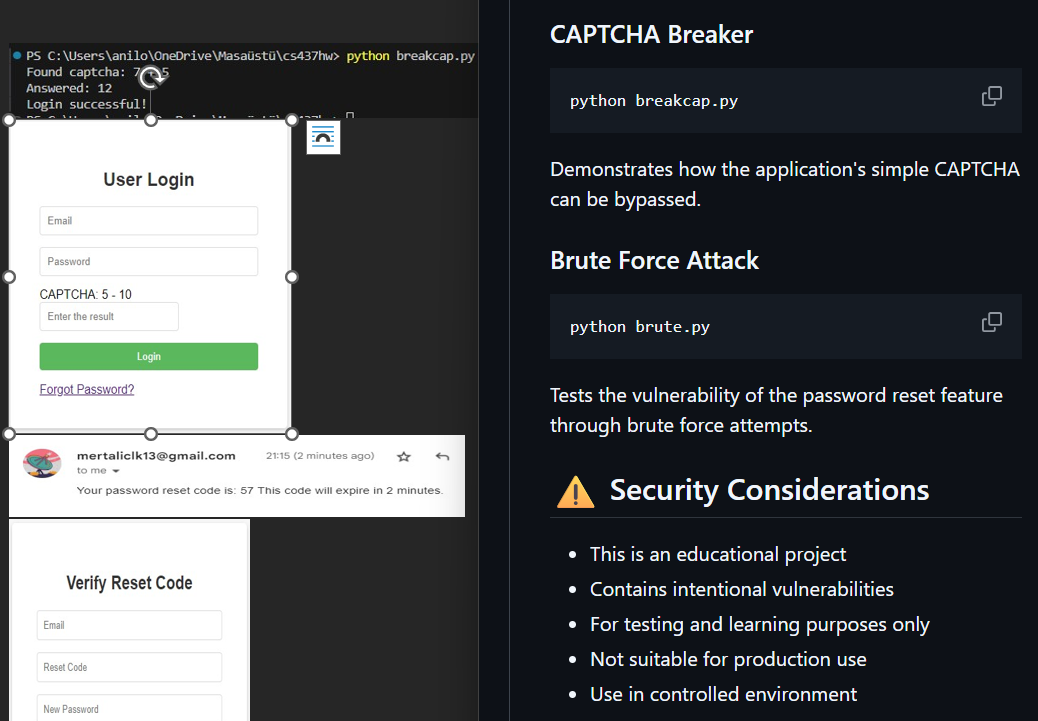
Designed a Flask-based web application with multiple attack surfaces, including authentication endpoints, comment submission forms, and admin panels, all instrumented with detailed logging. Used RSS feeds for dynamic content to make the site appear active and legitimate.
Key Challenges
- Making the honeypot convincing enough to attract real attacks
- Implementing comprehensive logging without impacting performance
- Securing the monitoring infrastructure from the attacks themselves
Results
Successfully deployed and captured multiple attack patterns including SQL injection attempts, credential stuffing, and XSS probes. Data used for security research and improving defensive strategies.